This position is based at our headquarters in Mooresville, North Carolina. Our corporate office is a space where you can collaborate and do your best work. Take a walk, grab a bite (or a cup of coffee), work out or get a check-up - we invest in you so you can find your inspiration.
Your Impact
The primary purpose of this role is to lead the implementation and ongoing delivery of information security tools and processes. This includes responsibility for creating, executing, and improving processes and procedures with limited direct guidance from more senior level security associates. This role solves complex problems while creating and optimizing processes and often takes a lead role in implementing new services and technologies. This role requires a strong understanding of most tools and processes supported by the team, including many of the key integration points with other parts of technology, works mostly independently, and provides coaching and direction to more junior level associates. When focused on Identity & Access Management (IAM), this role delivers timely, accurate, and controlled system access for the company's global workforce. This includes creating and maintaining processes, tools, controls, and governance mechanisms such as roles, reports, metrics, and issue resolution services. When focused on Security Architecture, this role is dedicated to the evaluation and enhancement of robust security solutions and frameworks. This includes developing and maintaining comprehensive security architectures, ensuring alignment with industry standards and best practices. When focused on Security Threat & Vulnerability, this role executes processes focused on vulnerability identification or remediation. This includes information security and risk activities such as oversight of vulnerability assessments and remediation programs serving both internal and external stakeholders. When focused on Security Governance, Risk, and Compliance (GRC), this role completes activities that help drive awareness and adherence to information security policies and standards.
What You Will Do
- Analyze data to detect trends, determine metrics, assess adherence to processes, make recommendations. and present results to information security and business leaders and/or vendors.
- Serve as an escalation point and mentor for junior staff.
- Maintain an awareness of information security news and trends and research current technologies to assist in development of new capabilities.
- Consolidate security related findings, track OKRs, and present results to information security and business leaders and/or vendors.
- Translate and document business needs into technical requirements and solutions.
- Advise users and team members on execution of processes, interpret standards and regulations, and assist with solutions.
- Identity & Access Management Responsibilities
- Create, execute, and improve processes and procedures in areas that include IAM, security policies, standards and controls creation and management, compliance management, risk management, training, and vulnerability assessment and remediation.
- Support IAM services by performing complex access provisioning, access reviews, role creation, and end user support.
- Complete high complexity account lifecycle management and application on-boarding to the IAM services, provisioning, access governance, role-based access creation, privileged access governance, and end user support for IAM and access-related service issues.
- Draft, apply, and interpret regulatory compliance standards and security policies, and advise on matters of compliance and solution options.
- Partner with senior key stakeholders to develop or update information security documents, such as policies, standards, procedures, and training.
- Security Threat & Vulnerability Responsibilities
- Create, execute, and improve processes and procedures in areas that include standards and controls creation and management, compliance management, risk management, training, and vulnerability assessment and remediation.
- Analyze complex technical and business requirements from a security perspective and make appropriate recommendations to reduce the over-all risk to the company.
- Security Governance, Risk, Compliance Responsibilities
- Design, develop and implement information security awareness and training programs tailored to the company's needs, objectives, and target audience.
- (governance) Establish, monitor, and update an effective information security governance framework that defines roles, responsibilities, and decision-making processes in collaboration with relevant stakeholders and in alignment with industry best practices.
- (governance) Implement and maintain a robust change and configuration management process, ensuring that all updates, revisions, and changes are documented, tracked, and approved in a systematic manner.
- (risk) Conduct online and onsite third-party risk assessments to identify and evaluate potential risks, including cybersecurity, regulatory compliance, financial stability, and operational risks.
- (risk) Work with vendors to address identified risks, establish risk mitigation plans, and monitor the implementation of remediation actions till closure. Ensure accurate and up-to-date records of assessments and associated risk mitigation activities.• (risk) Develop TPRM metrics and dashboard to provide visibility into the vendor's risk posture and recommend improvements.
- (compliance) Develop, implement, execute, and enhance the organization's IT compliance program. Ensure compliance with regulatory requirements, internal policies, and deadlines.
Minimum Qualifications
- Bachelor's degree in computer science, computer information systems, engineering, business administration, cybersecurity, or related field or equivalent years of experience in lieu of education requirement, if applicable
- 4 years of experience in information security
Preferred Skills/Education
- IT experience in the retail industry
- Hands-on experience on GRC applications & TPRM tools (e.g., Archer, LogicGate, SAP GRC, OneTrust, ProcessUnity, ServiceNow, BitSight, Prevalent, Black Kite, etc.)
- Experience with vulnerability identification & penetration testing tools
- Experience with vulnerability management in public/hybrid cloud environments.
- Experience with IAM technology implementation and operations (e.g., CA, Sailpoint, OKTA, SSO, MFA, IGA, Microsoft AD) (specific to IAM role)
- Experience developing cybersecurity or information assurance policies, standards, awareness training, or equivalent issuances (specific to Security GRC role)
- Payment Card Industry Internal Security Assessor (PCI ISA)
- Certified in Risk and Information Systems Control (CRISC)
- Offensive Security Certified Professional (OSCP)
- GIAC Penetration Tester Certification (GPEN)
- Practical Network Penetration Tester (PNPT)
- eLearnSecurity Certified Professional Penetration Tester (eCPPT)
- Certified Third-Party Risk Professional (CTPRP)
- Certified Third Party Risk Assessor (CTPRA)
- CompTIA PenTest+ Certification
- Or other relevant information security certifications
About Lowe's
Lowe's Companies, Inc. (NYSE: LOW) is a FORTUNE® 100 home improvement company with total fiscal 2025 sales of more than $86 billion. Lowe's employs approximately 300,000 associates and operates over 1,750 home improvement stores, 540 branches and 120 distribution centers. Based in Mooresville, N.C., Lowe's supports the communities it serves through programs focused on creating safe, affordable housing, improving community spaces, helping to develop the next generation of skilled trade experts and providing disaster relief to communities in need. For more information, visit Lowes.com .
Lowe's is an equal opportunity employer and administers all personnel practices without regard to race, color, religious creed, sex, gender, age, ancestry, national origin, mental or physical disability or medical condition, sexual orientation, gender identity or expression, marital status, military or veteran status, genetic information, or any other category protected under federal, state, or local law.
Skills Required
- Bachelor's degree in computer science or related field or equivalent experience
- 4 years of experience in information security
Lowe’s Compensation & Benefits Highlights
-
Inclusive Benefits Coverage — Medical, dental, and vision plans are available to regular full‑time and part‑time associates, with mental‑health resources also offered. Regular part‑time associates can also participate in the 401(k) with company match shortly after hire.
-
Retirement Support — A 401(k) with company match up to 4.25% when associates contribute 6% is available, with eligibility beginning shortly after employment. This supports long‑term savings across a broad set of roles and statuses.
-
Parental & Family Support — Up to 10 weeks paid maternity leave and 4 weeks paid parental leave are provided for eligible full‑time associates, alongside adoption assistance and fertility coverage. These offerings encompass both leave and family‑building support.
Lowe’s Insights

What We Do
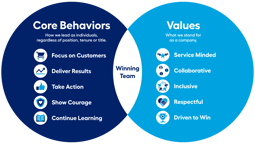
It’s curious to think of innovation and stability co-existing. But we pair a 100-year track record of success with a hunger to do things differently. Everyone is in the work — tackling complex problems where your impact can build back or build up the communities we serve. We fill our halls with curious minds from all walks of life. Our differences make us stronger, which is why our leaders build cultures of recognition and inclusion. You are heard, and your curiosities are celebrated and championed here.
Why Work With Us
We have built a space where the curious can move freely. Up in title, up in skills, to the side with teams, or back to try something completely new. We help you find your path — because when you win, we all win.
Gallery









Lowe’s Offices
Hybrid Workspace
Employees engage in a combination of remote and on-site work.