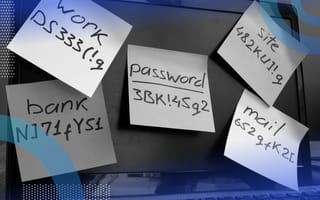
You have too many passwords, plain and simple. From banking apps to social media, from news sites to e-commerce, we all have a large and growing list of passwords to manage. Organizational passwords for enterprise resource planning (ERP), timesheets, learning management (the list goes on) only aggravates the problem.
With so many passwords to remember, bad password management is an inevitability.
How to Prevent a Data Breach: Avoid These Password Traps
- Reusing or slightly modifying passwords (i.e. “Password” to “P@ssword”) across systems.
- Poor password storage such as post-it notes on your desk, a spreadsheet on your computer or handwritten notes in a journal.
- Updated passwords that are only slightly different than ones you’ve previously used (e.g. “Password123” becomes “Password456”).
Each of these bad behaviors makes it that much easier for attackers to find their way into your systems and accounts. If you reuse your password across systems and one of those systems is compromised, you have to reset your password on every. single. system. If you keep your passwords on sticky notes near your computer — well, anyone walking by can access your account, of course. Finally, while incrementing the numbers in your password by one seems slick, if the previous credentials were breached, attackers will easily bypass your new password through attempting passwords similar to your old one.
A great resource to discover if your credentials have been compromised is www.haveibeenpwned.com but that’s a reactive approach. What proactive steps can you take now to protect yourself and your data?
Passwordless Authentication Methods
Future authentication technologies are looking more and more passwordless. Instead of relying on passwords for authentication, these systems use other secrets (also called factors).
Something You Know, Something You Are, Something You Have
Traditional passwords fall in the “something you know” category for authentication factors. Passwordless authentication replaces the password with some other factor and often uses a dual-factor system consisting of “something you are” and “something you have.” Examples of passwordless factors include fingerprints, facial scans, and FIDO2 keys. You are already likely using passwordless authentication for some systems.

Biometric Data
Facial scans are already popular on mobile phones; many applications allow you to use it to authenticate to their system. For example, Windows provides passwordless facial authentication with their “Hello” service. You can also find fingerprint scanners on mobile devices and laptops. These fall in the “something you are” and “something you have” categories, as the facial and fingerprint scans (something you are) are tied to the specific device doing the scanning (something you have).
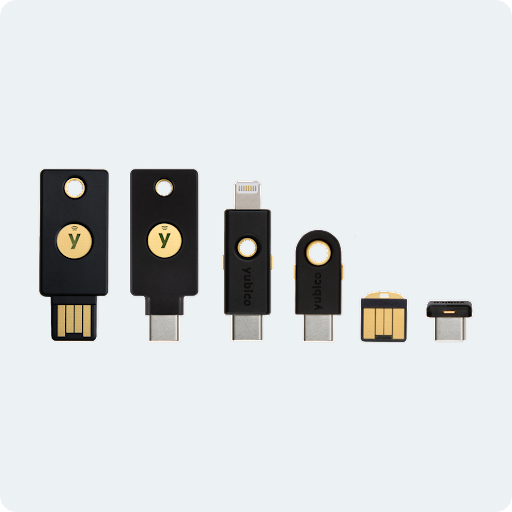
FIDO2 Keys
FIDO2 keys are hardware devices inserted into a device slot, or through near-field communication (NFC); they provide user authentication. These keys fall into the “something you have” category. Using these keys can improve the user experience by allowing the key to authenticate the user for any system that supports it. Instead of typing in a password, you simply plug the key in the device or hold it up to the NFC reader, and you’re in! Here are some common FIDO2 keys by the brand YubiKey.
However, moving to passwordless authentication technologies doesn’t come without challenges. Users are accustomed to using passwords. Making any technology shift, especially when they impact the end user experience, comes with the need for education and support costs. Users will likely require increased help desk support and training initiatives to successfully make the switch.
Passwordless authentication can also hinder the user experience when we design them with a single point of failure. For example, if you need a mobile phone to log in, the user may not be able to access their account if the device isn’t nearby or charged. We can avoid this by developing authentication systems to have multiple methods to log in, such as having the ability to authenticate using a facial scan or a FIDO2 key in addition to your mobile phone. This is more about how the system is set up than a limitation of the technology itself. Most directory systems should be able to support more than one authentication method — but only allowing one can cause user experience issues.
Exploring new authentication methods can improve both user experience and the security of your organization by reducing the number of passwords users must generate while also improving the speed (and accuracy) of security operations when responding to compromised credentials. While we’re seeing changes to the ways we use passwords, many systems still use traditional usernames and passwords for authentication. So how can we reduce the risk for those systems?
How to Improve Password Usage
While passwords have some flaws, there are some ways to mitigate these issues.
Multi-Factor Authentication (MFA)
Enabling multi-factor authentication (MFA) has one of the greatest impacts on reducing the risk of compromised passwords, with Microsoft studies showing MFA reduces the likelihood of compromised accounts by 99.9 percent. MFA adds one or more additional authentication factors in addition to the password. A common implementation of MFA requires you to log in and then enter a code sent over SMS or email. MFA has become a common practice for many widely used systems including Google, Amazon and AT&T so chances are you’ve encountered it before.
Not all MFA methods offer the same level of security. For example, inputting a pin sent over SMS is generally less secure than other methods. This relies on the assumption that the user is in possession of the device receiving SMS messages to that number, however that’s not always the case. SMS as an MFA is susceptible to SIM swap attacks, where an attacker convinces your phone carrier to switch your number to their device. Where feasible, use other factors such as hardware tokens, which use an algorithm to generate the PIN, or biometrics like facial scans and fingerprints.
When using pin-based MFA, it’s also important to ensure users remain aware of phishing attacks, as some attacks exist to bypass MFA. These attacks capture the user’s two-factor authentication token through a malicious website masquerading as a legitimate request. The attacker immediately uses the token to authenticate themselves. To learn more on how attackers accomplish this, check out the tool ReelPhish by security firm Mandiant.
Single Sign-On (SSO)
Single Sign-On (SSO), used in both the corporate and consumer landscapes, limits the number of disparate credentials you use. Reducing the number of credentials a user has significantly improves security by promoting the use of stronger passwords, proper password storage, easier password management and easier remediation in the event passwords become compromised.
Many large tech companies allow their authentication services to be used for SSO by other systems such as Google and Facebook. You have probably seen “Sign in with ____” prompts before.
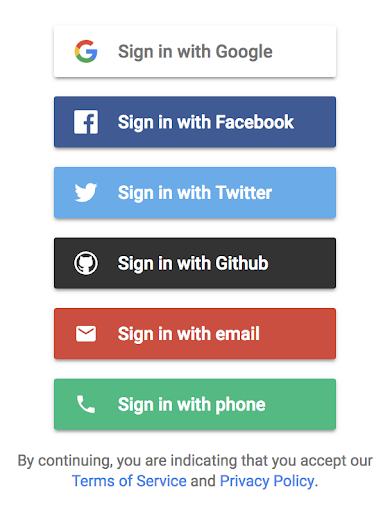
You can use Google, Facebook and Twitter as SSO providers to log in to the application. Users can also use a phone number or email address plus a traditional password as credentials. In enterprise implementations, SSO will usually use the organization’s existing directory service as the provider, such as Microsoft’s Active Directory.
SSO has some downsides, however. Because you use a single set of credentials across multiple systems, when an attacker gets their hands on them, they may be able to access other systems as well. You can mitigate this threat through attack surface reduction. In other words, use only a single authentication provider (e.g. only use Google to do SSO instead of switching between all possible SSO accounts). Heavily securing, monitoring and administering one authentication provider is often easier than doing the same for multiple. In addition, it’s imperative to use MFA when implementing SSO, so that even if a password is compromised, the attacker will still need a second factor to authenticate.
Password Managers
Password managers can also be used to alleviate some pain points. A password manager has the capability to securely store usernames and passwords for websites, generate secure passwords and autofill passwords on login forms. Your web browser or operating system likely has one built in, and more advanced third-party solutions exist like Dashlane and LastPass.
Password managers make it easier for users to implement unique and secure passwords as they don’t need to be memorized. Instead, the user only needs to remember a single, unique, complex password to get into the password manager. Password managers also make it easier for users to create complex passwords through automatically generated passcodes.
The future of authentication is looking more and more passwordless, but what does this mean for your organization? MFA should be the first thing you enable wherever possible. SMS or email pins may be adequate for some organizations, but other methods such as authentication apps or hardware tokens are best. SSO is worth taking a look at, as it will consolidate authentication to a single provider. SSO also means you can reduce IT costs because you’re supporting fewer authentication systems. From there, taking the jump to passwordless systems will set your organization up to support the next wave of authentication technology.
Opinions expressed are solely my own and do not express the views or opinions of my employer.
Frequently Asked Questions
What is passwordless authentication?
Passwordless authentication is a method used to verify user identity without the use of traditional passwords. It uses processes like biometrics or hardware keys to verify identity.
What are the main types of authentication factors?
Common types of authentication factors include something you know (e.g., a password), something you have (e.g., a FIDO2 key), and something you are (e.g., a fingerprint or facial scan).